Mega-cap tech stocks like Apple, Microsoft, and Amazon dominate markets with innovation in AI, cloud computing, and more, offering high-growth opportunities while influencing global financial trends and shaping future technologies.

The biggest hack in years involved several US agencies, 18,000 customers, and more than 425 of the Fortune 500, the US’ biggest companies.

The biggest hack in years involved several US agencies, 18,000 customers, and more than 425 of the Fortune 500, the US’ biggest companies.
Last year, SolarWinds, a small cybersecurity firm, was known for providing cyber solutions to larger companies, giving the firm a $6 billion valuation on $938.5 million in revenue. This week, it’s known as the company that single handedly gave suspected Russian cyber assailants access to over 18 thousand customers’ computers, up to 425 of the Fortune 500s’, and several federal agencies’. That makes this one of, if not the, biggest cyber breach to date.
Bombshell news was released on this Sunday about a major security breach that could have infected several hundreds customers across the world. This soon became much larger than originally expected, pushing into a reported number of customers making up 45% of the company’s 2020 revenue.
The hack was expected to have been completed through updates provided from SolarWinds, created by the cyber attackers. Through the company’s most popular software solution, Orion, a fake update attached to a backdoor through an avsvmcloud domain, was pushed out to all Orion customers, making one of the most secure portions of cyber security, one of its weakest.
Orion is used by organizations to install and monitor other SolarWinds products, over which there’s a huge suite provided by the company. SolarWinds CEO Kevin Thompson said in a statement to Reuters, that the breach was “a highly-sophisticated, targeted, and manual supply chain attack by a nation state.” While manual supply chain attacks, which manually insert malicious software through a company’s supply chain, aren’t very uncommon, something of this magnitude and invasiveness really is.
The amount of effort, time, and resources behind an attack of this magnitude is only possible through a large nation state, with most evidence pointing towards a Russian state sponsored attack on US software.
It’s believed that even though the breach was only discovered in December, that Russian hacks of SolarWinds began as far back as March, only coming to light when fellow cybersecurity firm, FireEye, disclosed a breach on December 9th. Since FireEye’s announcement, an exponentially growing list of victims has been identified, with some major inclusions being US Departments of State, Homeland Security, Commerce, Treasury, and Health.
This attack was devastating not only to the companies that were breached, or to the US, but to the US’ global ideal when it comes to security. The entire breach just goes to show that the US is not in fact as prepared as the company insists they are, including pointing out that the “newest” branch of military, Space Force, likely should have been a Cyber Force.
Reports are still coming in from the attack, since something of this scale having gone unnoticed for up to 9 months, means that any number of places or companies have been affected, with no real clue as to the entirety of the attack.
Some reports say that no classified information was taken, but nobody really knows for sure. US government officials have no clue what happened, where it happened, how it happened, when it happened, or how deep the breach went into the government.
The upsetting part for the federal government is their recent and complete belief into a project known as Einstein, a several dozen billion dollar program designed to detect and neutralize cyber threats. Even with all of that money, Einstein did nothing to prevent or discover this problem. (yet again, thanks FireEye)
Even with unsure depth of the attack, it’s been confirmed that the Department of Energy’s National Nuclear Security Administration, the Pentagon, and the previously mentioned Departments were compromised, as well as likely hundreds of private companies, including recently discovered Cisco Systems and Cox Communications.
The exact point of entry is very unclear. What we do know for sure, is that state sponsored cyber actors (Russia denies their involvement) gained access to SolarWinds Orion tools, and forced an update down the pipeline, affecting tens of thousands of people and companies.
Really, the thing that matters is that these actors didn’t need phishing or stolen credentials, individual access or ransomware to access thousands of customers. By gaining access to an update protocol, they managed to upload malware that affected thousands of computers, without the company that created the software finding out. Microsoft didn’t find out, Einstein didn’t find out, the US government didn’t find out, SolarWinds didn’t find out, thousands of companies didn’t find out, and nobody likely would have even noticed except for the fact that FireEye traced the hack from their systems back to SolarWinds, then to foreign actors.
The thing that matters is that none of that was needed because SolarWinds was the actors’ tool into these systems. SolarWinds’ Orion has high administrative powers, helping the actors gain high powered access to high level software without even doing anything differently. By using naturally possessed administrative powers, they just needed to include a single link to malicious software within the update.
Apparently SolarWinds has actually persuaded many of its customers that they need not fret with antivirus and security restrictions when it came to their technology, such as Orion, as Orion products would have likely been viewed as a threat, due to its wide reaching administrative powers. This part makes sense as security marking other security as a threat has been around for a while, and it really needs a fix.
Overall, the access that intruders had gained through SolarWinds updates is farther reaching than the actual access gained by said software compromises, as the companies that were affected, affected the companies that they worked for, and the customers that hired said company, and the breach’s reach only seems to be spreading when taking into each company’s individual reach.
As we continue to find out more about this apparently long lasting breach, there’s likely to be long lasting effects as well, such as the US government assuming that many of its computer systems are still compromised, with no end to this in sight.

Mega-cap tech stocks like Apple, Microsoft, and Amazon dominate markets with innovation in AI, cloud computing, and more, offering high-growth opportunities while influencing global financial trends and shaping future technologies.

CoreWeave posted exceptional Q1 2025 results with revenue reaching $981.6 million, up 420% year-over-year. The AI infrastructure provider secured key partnerships with OpenAI and IBM, while maintaining a 62% Adjusted EBITDA margin. The company’s revenue backlog grew to $25.9 billion, bolstered by OpenAI’s $11.2 billion strategic commitment.

E-commerce giant Shopify delivered exceptional Q1 2025 results with revenue up 27% to $2.36B and operating income doubling to $203M, while maintaining strong merchant growth and platform adoption.
The biggest hack in years involved several US agencies, 18,000 customers, and more than 425 of the Fortune 500, the US’ biggest companies.

The biggest hack in years involved several US agencies, 18,000 customers, and more than 425 of the Fortune 500, the US’ biggest companies.
Last year, SolarWinds, a small cybersecurity firm, was known for providing cyber solutions to larger companies, giving the firm a $6 billion valuation on $938.5 million in revenue. This week, it’s known as the company that single handedly gave suspected Russian cyber assailants access to over 18 thousand customers’ computers, up to 425 of the Fortune 500s’, and several federal agencies’. That makes this one of, if not the, biggest cyber breach to date.
Bombshell news was released on this Sunday about a major security breach that could have infected several hundreds customers across the world. This soon became much larger than originally expected, pushing into a reported number of customers making up 45% of the company’s 2020 revenue.
The hack was expected to have been completed through updates provided from SolarWinds, created by the cyber attackers. Through the company’s most popular software solution, Orion, a fake update attached to a backdoor through an avsvmcloud domain, was pushed out to all Orion customers, making one of the most secure portions of cyber security, one of its weakest.
Orion is used by organizations to install and monitor other SolarWinds products, over which there’s a huge suite provided by the company. SolarWinds CEO Kevin Thompson said in a statement to Reuters, that the breach was “a highly-sophisticated, targeted, and manual supply chain attack by a nation state.” While manual supply chain attacks, which manually insert malicious software through a company’s supply chain, aren’t very uncommon, something of this magnitude and invasiveness really is.
The amount of effort, time, and resources behind an attack of this magnitude is only possible through a large nation state, with most evidence pointing towards a Russian state sponsored attack on US software.
It’s believed that even though the breach was only discovered in December, that Russian hacks of SolarWinds began as far back as March, only coming to light when fellow cybersecurity firm, FireEye, disclosed a breach on December 9th. Since FireEye’s announcement, an exponentially growing list of victims has been identified, with some major inclusions being US Departments of State, Homeland Security, Commerce, Treasury, and Health.
This attack was devastating not only to the companies that were breached, or to the US, but to the US’ global ideal when it comes to security. The entire breach just goes to show that the US is not in fact as prepared as the company insists they are, including pointing out that the “newest” branch of military, Space Force, likely should have been a Cyber Force.
Reports are still coming in from the attack, since something of this scale having gone unnoticed for up to 9 months, means that any number of places or companies have been affected, with no real clue as to the entirety of the attack.
Some reports say that no classified information was taken, but nobody really knows for sure. US government officials have no clue what happened, where it happened, how it happened, when it happened, or how deep the breach went into the government.
The upsetting part for the federal government is their recent and complete belief into a project known as Einstein, a several dozen billion dollar program designed to detect and neutralize cyber threats. Even with all of that money, Einstein did nothing to prevent or discover this problem. (yet again, thanks FireEye)
Even with unsure depth of the attack, it’s been confirmed that the Department of Energy’s National Nuclear Security Administration, the Pentagon, and the previously mentioned Departments were compromised, as well as likely hundreds of private companies, including recently discovered Cisco Systems and Cox Communications.
The exact point of entry is very unclear. What we do know for sure, is that state sponsored cyber actors (Russia denies their involvement) gained access to SolarWinds Orion tools, and forced an update down the pipeline, affecting tens of thousands of people and companies.
Really, the thing that matters is that these actors didn’t need phishing or stolen credentials, individual access or ransomware to access thousands of customers. By gaining access to an update protocol, they managed to upload malware that affected thousands of computers, without the company that created the software finding out. Microsoft didn’t find out, Einstein didn’t find out, the US government didn’t find out, SolarWinds didn’t find out, thousands of companies didn’t find out, and nobody likely would have even noticed except for the fact that FireEye traced the hack from their systems back to SolarWinds, then to foreign actors.
The thing that matters is that none of that was needed because SolarWinds was the actors’ tool into these systems. SolarWinds’ Orion has high administrative powers, helping the actors gain high powered access to high level software without even doing anything differently. By using naturally possessed administrative powers, they just needed to include a single link to malicious software within the update.
Apparently SolarWinds has actually persuaded many of its customers that they need not fret with antivirus and security restrictions when it came to their technology, such as Orion, as Orion products would have likely been viewed as a threat, due to its wide reaching administrative powers. This part makes sense as security marking other security as a threat has been around for a while, and it really needs a fix.
Overall, the access that intruders had gained through SolarWinds updates is farther reaching than the actual access gained by said software compromises, as the companies that were affected, affected the companies that they worked for, and the customers that hired said company, and the breach’s reach only seems to be spreading when taking into each company’s individual reach.
As we continue to find out more about this apparently long lasting breach, there’s likely to be long lasting effects as well, such as the US government assuming that many of its computer systems are still compromised, with no end to this in sight.

Mega-cap tech stocks like Apple, Microsoft, and Amazon dominate markets with innovation in AI, cloud computing, and more, offering high-growth opportunities while influencing global financial trends and shaping future technologies.

CoreWeave posted exceptional Q1 2025 results with revenue reaching $981.6 million, up 420% year-over-year. The AI infrastructure provider secured key partnerships with OpenAI and IBM, while maintaining a 62% Adjusted EBITDA margin. The company’s revenue backlog grew to $25.9 billion, bolstered by OpenAI’s $11.2 billion strategic commitment.

E-commerce giant Shopify delivered exceptional Q1 2025 results with revenue up 27% to $2.36B and operating income doubling to $203M, while maintaining strong merchant growth and platform adoption.
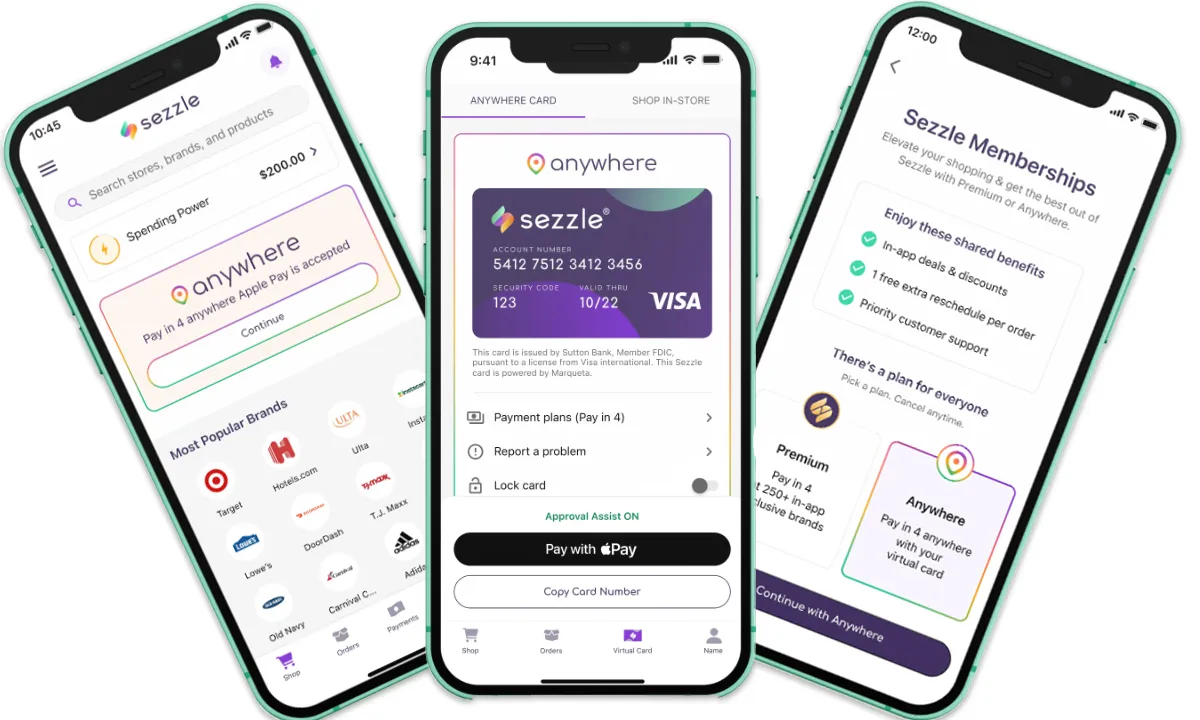
Buy-now-pay-later leader Sezzle shattered Q1 expectations with revenue surging 123% to $104.9M, as net income quadrupled to $36.2M. The fintech company raised 2025 guidance on strong performance across all metrics.